THE PROBLEM
Modern cyber threat intelligence suffers from fragmentation.
Data is scattered across dozens of tools, feeds and platforms - each providing only a small fragment of the overall picture.
Analysts are forced to manually correlate infrastructure, campaigns, actors and indicators across disconnected systems.
Threat actors, however, operate as systems.
They move across infrastructure, malware and campaigns, constantly adapting while maintaining underlying patterns.
Understanding them requires more than collecting data.
It requires modeling relationships and tracking evolution over time.
Indicators appear in feeds and disappear days later.
Connections between infrastructure are rarely preserved.
Signals are processed in isolation.
Without context, intelligence becomes noise.
Without relationships, analysis becomes guesswork.
THE INTELLIGENCE GAP
Adversaries operate as systems
Understanding requires observing relationships.
Tracking evolution over time.
Linking infrastructure, campaigns and actors.
ACTOR-CENTRIC INTELLIGENCE
Collects domains, IPs and hashes
Treats indicators as isolated data points
Limited context
No persistent relationships
Hard to track evolution
Links artifacts back to the actor
Models infrastructure as a system
Tracks relationships over time
Campaigns become comparable
Behavior becomes predictable
Kraken shifts analysis from collecting indicators to understanding adversaries.
Not just what happened, but who is behind it, how they operate, and where they are likely to move next.
THE KRAKEN APPROACH
From indicators to systems
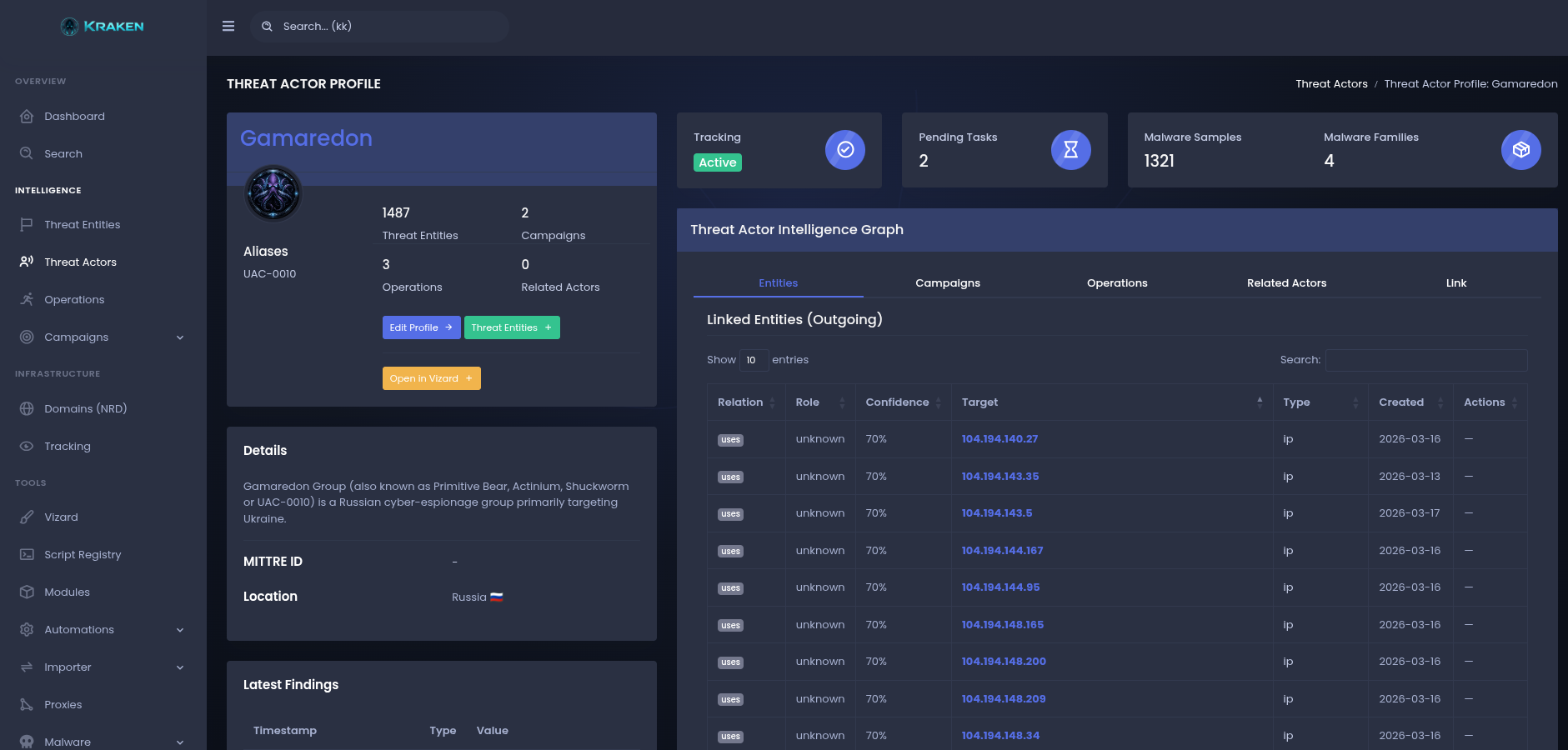
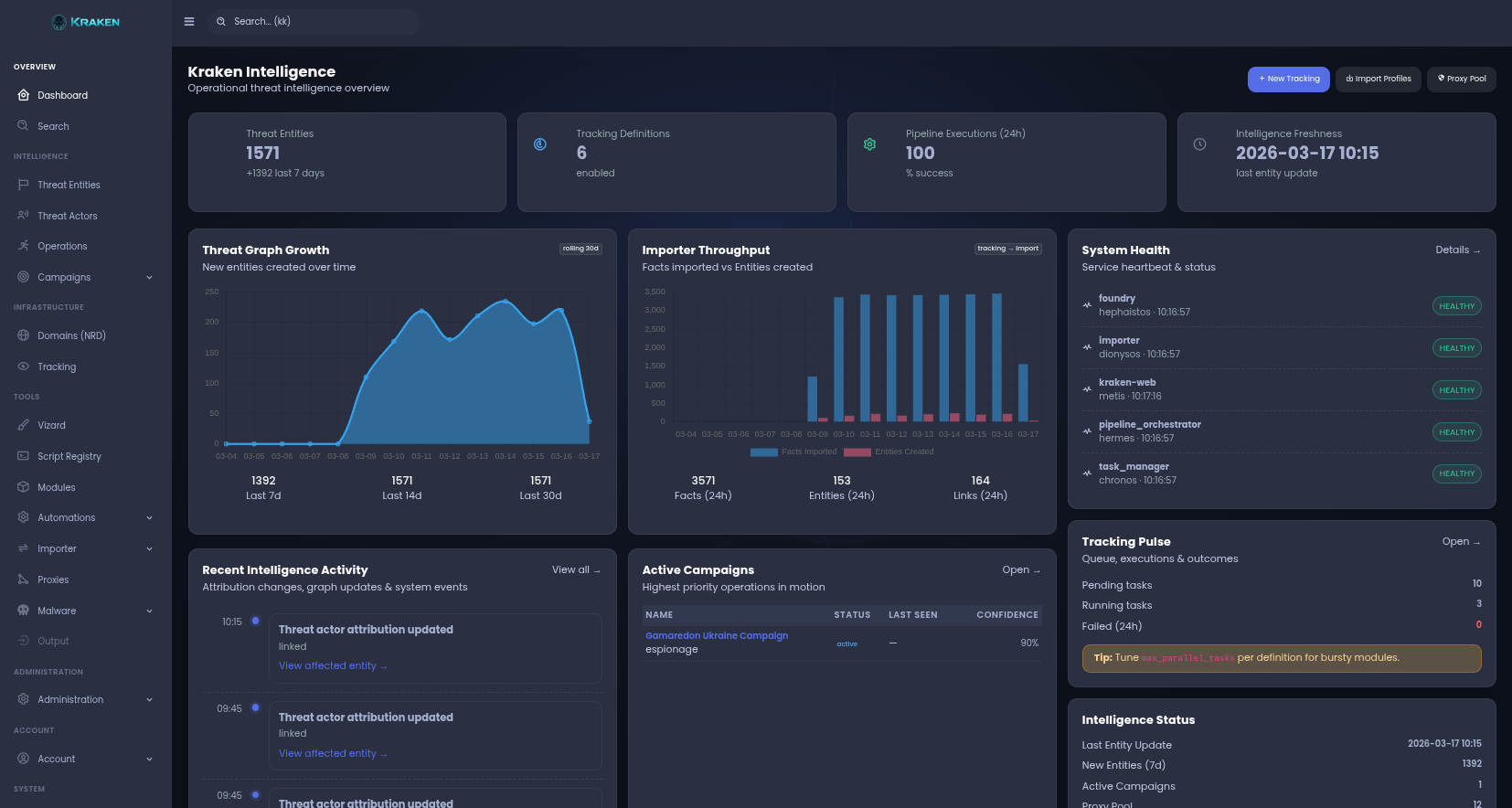
Kraken is a modular threat intelligence platform designed to continuously collect, model and analyze adversary infrastructure.
Instead of focusing on isolated indicators, Kraken builds a living intelligence graph.
Every domain, IP, malware sample or campaign becomes part of a larger system.
Continuous intelligence pipeline
Tracking definitions monitor entities and trigger collection workflows.
Collection modules gather intelligence across multiple sources.
Results are normalized and linked into the intelligence graph.
The system continuously expands its understanding of the threat landscape.
HOW IT ACTUALLY WORKS
1 domain / IP / artifact
automated tracking pipeline
+27 domains
+12 IPs
+3 dead drops
WHY KRAKEN
CORE CAPABILITIES
DATA & MODELING
- Entity modeling (malware, actors, campaigns, domains, IPs)
- Relationship graph (infrastructure, links, dependencies)
- Threat actor clustering
- Campaign & actor analysis over time
COLLECTION & PIPELINE
- Continuous infrastructure tracking
- Automated collection pipelines
- Modular collectors & enrichment modules
- Automated graph expansion
INTELLIGENCE & ANALYSIS
- Real-time pipeline monitoring
- Operational intelligence dashboards
- Behavioral pattern detection
- Infrastructure correlation
EXTENSIBILITY
- Custom module integration
- Script-based collection (Script Runner)
- Flexible data ingestion
- Scalable architecture
VISION
From fragmented data to structured intelligence.
Kraken provides analysts with a system capable of mapping the hidden infrastructure behind global cyber operations.
Where signals form patterns.
Where data becomes intelligence.
Where adversary activity becomes visible.
Threat actors operate in the deep.
Kraken reveals what moves beneath the surface.
PRACTICAL USE CASES
Click for detailsProblem: IOC lists break quickly.
Use: Track infrastructure as evolving graph.
Outcome: No more chasing expired IOCs.
Use: Start from single artifact and expand automatically.
Outcome: Faster containment and scoping.
Use: Track domains and actors over time.
Outcome: From reactive → proactive detection.
Use: Detect Telegram / DNS hidden channels.
Outcome: Visibility into hidden comms.
Use: Automate enrichment and correlation.
Outcome: Raw data → intelligence graph.
Use: Model actors instead of indicators.
Outcome: Strategic understanding.
WHITEPAPER
The Kraken Whitepaper provides a detailed overview of the platform architecture, threat intelligence modeling approach and the continuous collection pipeline used to track adversary infrastructure.
It explains how Kraken transforms fragmented cyber threat data into a structured intelligence graph and how analysts can model campaigns, actors and infrastructure over time.
ACCESS
Kraken is not a public intelligence platform.
Access to the system is restricted and requires analyst vetting.
Each request is manually reviewed to ensure that the platform
remains dedicated to trusted researchers, defenders and institutions.
If you are interested in evaluating Kraken, you may initiate the access request process below.